I set up ssh u2f login with Trezor one. It was easy, but I’m very disappointed, that it also works when the device is not unlocked. It’s not any safer than yubikey.
Can it be enabled somehow? It should be enabled by default. It would make ssh login safer by several magnitudes. I don’t understand how could satoshilabs make such mistake.
1 Like
you can use trezor-agent for SSH, which will be PIN-locked and optionally even passphrase protected.
the problem with U2F is that it doesn’t have any means of passing through Trezor One’s pin entry. there is no driver that could hook into the u2f protocol to interject a visual pin entry dialog every time a website makes your yubikey flash its light. for this reason, U2F on T1 needs to work without pin.
or you can upgrade to Trezor T which has on-device pin entry that also works for fido2 and u2f
1 Like
The pin can be entered before ssh login, so the push button would work only then, making it much safer. Exactly same like suite is working.
1 Like
That would mean that (a) you need to install Suite to be able to use u2f at all, and (b) every time your device locks, you would need to go to Suite to unlock it manually before being able to use the u2f feature, with the only possible indication that something is wrong on the Trezor screen, on which the user might not be looking at the time.
Usability would suffer – and as the saying goes, security at the cost of usability comes at the cost of security.
The main threat model for U2F is remote, and against that, pin-less devices such as yubikey work perfectly fine. Again, if you want greater security, you can use trezor-agent, or get a Model T.
1 Like
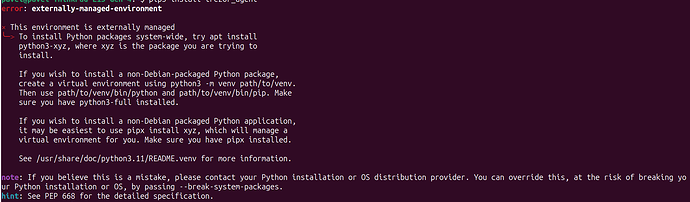
Is this trezor.io/learn/a/ssh-with-trezor right docu to install trezor -agent? it says Ubuntu 18.04 LTS, and does not work on ubuntu 23.04
is there apk to download? or better PPA repo?
forum without links?
1 Like
yes
unfortunately, no. I suggest going with pipx that the text you see recommends.
thanks for the info. we’ll see if we can get the instructions updated
2 Likes